Mail Order Brides, Pornography & Malware: How Website Hacks Can Hit Your Business
by Will Williamson on 28-Dec-2022 11:30:00

Cyber-attacks don’t just affect large banks and the NHS, they affect smaller businesses, too. Stats vary, but a 2020 UK Government survey of cybercrime against SMEs reported that 46% of respondents had experienced an attempted cyber-attack in that year. Organisations most at risk were mid-sized businesses, large businesses, and high-income charities.
Even though most attempted cyber-attacks don’t result in a breach, cybercrime is clearly something that is common enough to be worried about. And what would happen to your business should a breach occur? Most blogs on the subject focus on the monetary implications of cybercrime – ransomware, identity theft directed at employees and customers, and financial fraud – but cybercrime can also be plain embarrassing.
Cuckoo Content
Two of our own clients recently had their websites hacked in damaging and extremely embarrassing ways, costing time, money, and reputation to resolve. Both are established, small-to-mid-sized professional service companies with an active online customer base.
In both cases, the hacker or hackers managed to breach the business’s website security and replace some or all of their content with dubious third-party material – so-called ‘cuckoo content’.
- Client #1 (a firm of solicitors) was surprised to discover a huge volume of pornographic images and videos posted on their site, replacing the pre-existing contact.
- Client #2 (a document shredding service) found themselves the unwitting host of over 700 articles relating to ‘mail order’ brides and overseas dating. The cuckoo content was sufficient for the company website to rank highly on Google for the evocative keywords ‘Cambodian cupid’ and ‘Ukrainian brides.’
Why Them?
Setting aside the humorous nature (in retrospect, at least) of the hacks, the question remains – why them?
Neither is a particularly large or prominent business or an obvious target for extortion. Both follow standard web security practices common to businesses across the UK, and neither could recall a recent attempt at a breach, or anyone having clicked a phishing email or text.
In these cases, the point of vulnerability wasn’t a weak password, compromised social media account, or email server – it was the business website itself.
Open Source, Open Access
To be clear, JDR did not build or maintain these company websites. They were each built using open-source software (WordPress in one case, Expression Engine in the other) and were hosted using a third-party hosting service.
It was a vulnerability in the open-source code of each website that allowed the hacker to exploit a backdoor entrance into the customer’s browser-based dashboard, from which he or she could manipulate the customer’s content.
Unfortunately, the popularity and strength of open-source software – the fact that the source code is openly available to all developers and is not owned and managed by a proprietary company – is also its greatest Achilles Heel.
A cyber-criminal can access the source code in the same way as an app developer or designer can – and with no centralised oversight and update strategy, there is very little that users can do to close the door to any security loopholes in the software. Malware code can quite easily be written into the source code of a bogus app or plug-in, allowing criminals access to a company’s website.
What is the solution?
Open-source websites are not inherently insecure, but their dependence on community trust and independent developers is a clear weakness in some cases, especially for websites that are not regularly updated with the latest security best practices.
We are increasingly of the opinion that proprietary Software as a Service (SaaS) websites offer better security for businesses than open-source sites. This is because SaaS website vendors (such as HubSpot, Shopify, and Squarespace) use a ‘closed’ and closely guarded code that isn’t open to developers outside of the company. It is far harder for a cyber-criminal to exploit weaknesses in a code that is locked away and regulated under central supervision in this way.
Furthermore, should weaknesses be identified, it is far easier in a SaaS system for the proprietor to identify flaws and take swift remedial reactions to improve security. It’s not that cyber criminals don’t attempt to target SaaS-built websites – they do – simply that proprietary website developers are better placed to stay one step ahead of cyber-attacks with pro-active updates, and to close security loopholes that in open-source software may remain open indefinitely.
Find out more
The risk of a cyber-attack on your business isn’t something you can entirely avoid, but you can take steps to make it more difficult for criminals to target your business – and upgrading to a more secure framework for your website is an important first step.
To find out more about what you can do, and why you may need to review your current website security safeguards, please call our web development team today on 01332 529260.
Image Source: Pexels
- Inbound Marketing (SEO, PPC, Social Media, Video) (838)
- Strategy (371)
- Sales & CRM (198)
- Marketing Automation & Email Marketing (193)
- Business Growth (168)
- Website Design (165)
- Hubspot (145)
- Lead Generation (118)
- Google Adwords (100)
- Content Marketing (94)
- Conversion (55)
- Case Studies (54)
- News (47)
- Ecommerce (39)
- Webinars (37)
- SEO (29)
- AI (21)
- Events (20)
- LinkedIn Advertising (17)
- Video (17)
- Video Selling (15)
- Software training (13)
- Niche business marketing (12)
- HubSpot Case Studies (10)
- The Digital Prosperity Podcast (10)
- Facebook Advertising (8)
- Web Design Case Studies (3)
- April 2026 (9)
- March 2026 (7)
- February 2026 (13)
- January 2026 (12)
- December 2025 (15)
- November 2025 (6)
- October 2025 (17)
- September 2025 (16)
- August 2025 (14)
- July 2025 (14)
- June 2025 (5)
- May 2025 (19)
- April 2025 (15)
- March 2025 (13)
- February 2025 (13)
- January 2025 (8)
- December 2024 (2)
- November 2024 (4)
- October 2024 (21)
- September 2024 (4)
- August 2024 (8)
- July 2024 (14)
- June 2024 (16)
- May 2024 (25)
- April 2024 (15)
- March 2024 (18)
- February 2024 (5)
- January 2024 (10)
- December 2023 (6)
- November 2023 (10)
- October 2023 (13)
- September 2023 (12)
- August 2023 (14)
- July 2023 (13)
- June 2023 (14)
- May 2023 (15)
- April 2023 (13)
- March 2023 (14)
- February 2023 (13)
- January 2023 (15)
- December 2022 (13)
- November 2022 (6)
- October 2022 (8)
- September 2022 (22)
- August 2022 (15)
- July 2022 (13)
- June 2022 (16)
- May 2022 (14)
- April 2022 (16)
- March 2022 (17)
- February 2022 (11)
- January 2022 (8)
- December 2021 (6)
- November 2021 (7)
- October 2021 (11)
- September 2021 (10)
- August 2021 (7)
- July 2021 (7)
- June 2021 (4)
- May 2021 (4)
- April 2021 (1)
- March 2021 (3)
- February 2021 (5)
- January 2021 (4)
- December 2020 (7)
- November 2020 (6)
- October 2020 (5)
- September 2020 (9)
- August 2020 (18)
- July 2020 (17)
- June 2020 (17)
- May 2020 (10)
- April 2020 (21)
- March 2020 (24)
- February 2020 (20)
- January 2020 (12)
- December 2019 (23)
- November 2019 (12)
- October 2019 (14)
- September 2019 (16)
- August 2019 (15)
- July 2019 (13)
- June 2019 (6)
- May 2019 (8)
- April 2019 (4)
- March 2019 (2)
- February 2019 (2)
- January 2019 (2)
- December 2018 (3)
- November 2018 (24)
- September 2018 (11)
- August 2018 (9)
- June 2018 (3)
- May 2018 (6)
- April 2018 (14)
- March 2018 (12)
- February 2018 (16)
- January 2018 (15)
- December 2017 (15)
- November 2017 (18)
- October 2017 (23)
- September 2017 (19)
- August 2017 (28)
- July 2017 (27)
- June 2017 (25)
- May 2017 (18)
- April 2017 (17)
- March 2017 (16)
- February 2017 (17)
- January 2017 (14)
- December 2016 (21)
- November 2016 (27)
- October 2016 (25)
- September 2016 (16)
- August 2016 (20)
- July 2016 (19)
- June 2016 (14)
- May 2016 (20)
- April 2016 (24)
- March 2016 (22)
- February 2016 (28)
- January 2016 (27)
- December 2015 (28)
- November 2015 (19)
- October 2015 (9)
- September 2015 (12)
- August 2015 (5)
- July 2015 (1)
- June 2015 (10)
- May 2015 (3)
- April 2015 (11)
- March 2015 (14)
- February 2015 (15)
- January 2015 (12)
- December 2014 (2)
- November 2014 (23)
- October 2014 (2)
- September 2014 (2)
- August 2014 (2)
- July 2014 (2)
- June 2014 (7)
- May 2014 (14)
- April 2014 (14)
- March 2014 (7)
- February 2014 (2)
- January 2014 (7)
- December 2013 (9)
- November 2013 (14)
- October 2013 (17)
- September 2013 (3)
- August 2013 (6)
- July 2013 (8)
- June 2013 (4)
- May 2013 (3)
- April 2013 (6)
- March 2013 (6)
- February 2013 (7)
- January 2013 (5)
- December 2012 (3)
- November 2012 (2)
- September 2012 (1)
Subscribe by email
You May Also Like
These Related Blogs

How To Ensure Your Company's Marketing Activities Are GDPR-Compliant
The European Union's General Data Protection Regulation (GDPR) came into force on 25th May 2018 and affects both individuals and businesses within the …

Can Your Competition Cost You Money In Google AdWords?
Google AdWords is a brilliant online advertising platform that many businesses take advantage of. The biggest benefit being that it allows smaller com …
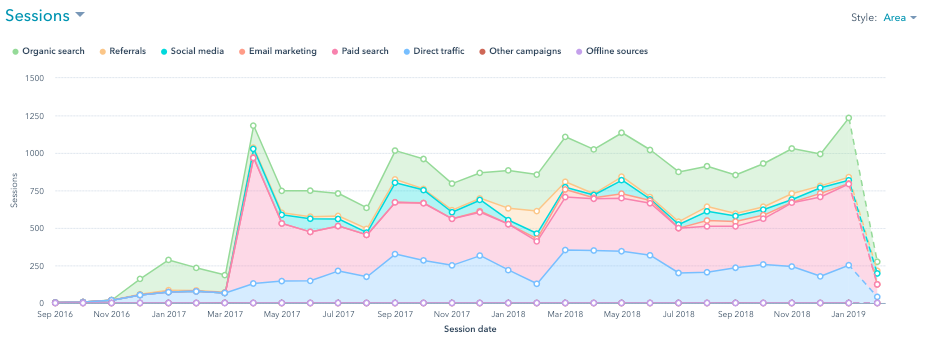
Digital Marketing For Manufacturing Business [Case Study] - Specialist Manufacturers Generate £3.6m Revenue And 5x Increase In Website Traffic
Key Results £3.6m in directly attributable revenue from marketing 5x increase in website traffic Rebrand with new logo, new branding, new brochures Ha …